The hidden chain of compromised modules that silently infected developers’ builds.
On the morning of September 8, 2025, attackers took control of a famous npm developer’s account using social engineering techniques. They published hacked versions of very popular npm packages including debug and chalk. The attack lasted just a couple of hours before it was detected and dealt with, but that short window was enough for some developers and companies to accidentally include the poisoned packages in their apps. If these apps served web content, any browser that loaded the affected website risked activating hidden malware that could hijack cryptocurrency transactions and send funds to criminals. Even though the immediate damage in terms of stolen crypto was said to be minimal, the event triggered a major scramble across the tech world to verify and patch software dependencies.
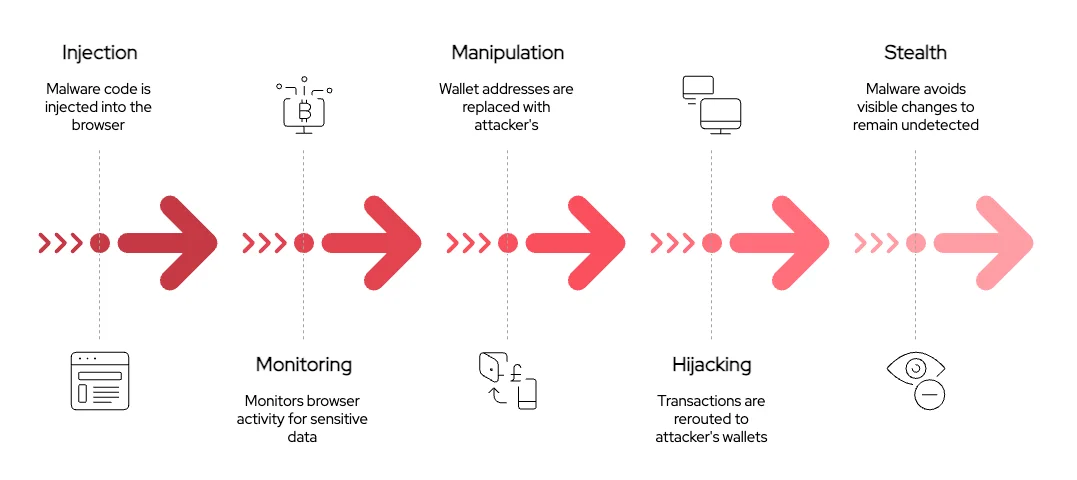
How the Infection Worked
A developer or automated build process that installed the malicious versions would end up bundling the bad code with their application. The payload then ran in users’ browsers if they visited affected sites. The code quietly watched for crypto wallet interactions like MetaMask or Solana, waiting for someone to try to send tokens. Right when the person clicked to confirm a transaction, the malware would sneak in, rewrite destination addresses and approvals, so that instead of going to the intended recipient, the money was silently sent to the hackers. Most users would never notice because everything looked normal on the screen.

Impact on Finance and Technology
Finance and tech were especially exposed in this attack. Many web apps move crypto, digital payments, or manage wallets directly from the browser. With so much modern banking and trading relying on JavaScript packages, poisoned dependencies might put huge sums at risk. The malware was built to specifically intercept and manipulate crypto transactions, so anyone dealing with cryptocurrency or digital payments, even big fintech firms had reason to worry. While the direct losses were limited this time, trust in open-source software supply chains took a heavy blow, and the need for fast, industry-wide response became clear.
Timeline and Community Response
Once the attack was discovered, security teams and maintainers moved quickly to yank the malicious versions from npm. Companies used dependency scanning tools to search their codebases for affected packages and began purging any tainted code from their servers and continuous integration systems. By the afternoon, most traces of the attack had been identified, but teams across the world spent countless hours auditing, rebuilding, and locking down their systems. The security community shared real-time updates and provided scripts to help businesses find and fix risky dependencies as fast as possible.

Why It Matters & Lessons Learned
This attack highlighted just how much of modern finance, everyday apps, and even critical banking infrastructure depends on open-source software that anyone can upload and update. A single compromised maintainer account let hackers sneak harmful code into billions of potential downloads. To defend against these threats, companies are being urged to use lockfiles, audit their dependencies, implement alerts, and verify emails, especially any related to security or two-factor authentication. Fast response, automated tooling, and global collaboration are now vital to keep tech and finance safe in a world where one phishing email can jeopardize vast amounts of money and trust.
Purv Kabaria